- Home
- Social networking
- Social networking News
- Check for compromised LinkedIn passwords using LeakedIn web app
Check for compromised LinkedIn passwords using LeakedIn web app
By Gurman Bhatia | Updated: 7 June 2012 21:14 IST
Click Here to Add Gadgets360 As A Trusted Source

Advertisement
Reports of 6.5 million LinkedIn password hashes being leaked for certain users went out this Wednesday. Users are both concerned and apprehensive about the fact that whether they are a victim as well.
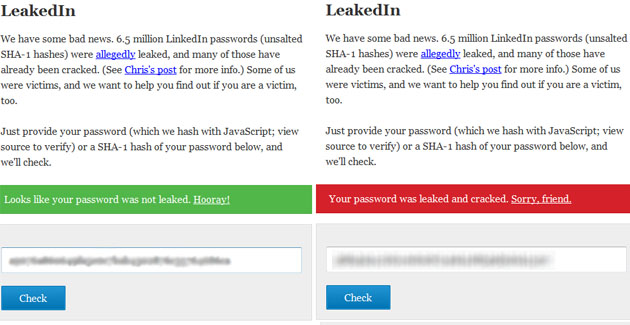
With the amount of personal and professional information available on this platform, the growing concern led 'LeakedIn' to emerge. A New York based web developer has come out with a web app 'LeakedIn' that allows users to check whether their LinkedIn password has been compromised. All one needs to do, is enter their password in a dialog box and it then converts it into its corresponding cryptographic representation using the SHA-1 algorithm, which was stored by LinkedIn. Matching your password hash with the leaked hashes, it tells you whether your password has been comprised or not. It does that conversion in the browser using JavaScript and does not transmit the password elsewhere, wrote one of LeakedIn's developers, Chris Shiflett, on his blog.
The issue in hand is the fact that whether the leaked passwords has been 'cracked' as well. Not all of the hashes in the list have been converted to original passwords yet, but hackers are likely to be working on it. The number of characters in your password would determine the amount of time the 'cracking' would require.
This massive leak of passwords is an effect of LinkedIn using unsalted hashes. Salting is a process that involves inserting random characters into the hash that make it more difficult for people trying a brute-force attack.
LinkedIn on its official blog has responded to the fears mentioning customer security as its primary concern and stating that all the users whose passwords have been compromised would soon receive an email asking them for a password reset. These emails will not have direct links for password reset, but will include a multi-step process to verify the user. LinkedIn also states that it would now be working on 'salting' its password hashes. This enormous breach has brought extreme disappointment amidst the users.
Editor's note: You should change your LinkedIn password before you use LeakedIn and then enter your old password to see if your password was leaked. We do not recommend sharing your current LinkedIn (or any other) password with any third-party website.
With the amount of personal and professional information available on this platform, the growing concern led 'LeakedIn' to emerge. A New York based web developer has come out with a web app 'LeakedIn' that allows users to check whether their LinkedIn password has been compromised. All one needs to do, is enter their password in a dialog box and it then converts it into its corresponding cryptographic representation using the SHA-1 algorithm, which was stored by LinkedIn. Matching your password hash with the leaked hashes, it tells you whether your password has been comprised or not. It does that conversion in the browser using JavaScript and does not transmit the password elsewhere, wrote one of LeakedIn's developers, Chris Shiflett, on his blog.
The issue in hand is the fact that whether the leaked passwords has been 'cracked' as well. Not all of the hashes in the list have been converted to original passwords yet, but hackers are likely to be working on it. The number of characters in your password would determine the amount of time the 'cracking' would require.
This massive leak of passwords is an effect of LinkedIn using unsalted hashes. Salting is a process that involves inserting random characters into the hash that make it more difficult for people trying a brute-force attack.
LinkedIn on its official blog has responded to the fears mentioning customer security as its primary concern and stating that all the users whose passwords have been compromised would soon receive an email asking them for a password reset. These emails will not have direct links for password reset, but will include a multi-step process to verify the user. LinkedIn also states that it would now be working on 'salting' its password hashes. This enormous breach has brought extreme disappointment amidst the users.
Editor's note: You should change your LinkedIn password before you use LeakedIn and then enter your old password to see if your password was leaked. We do not recommend sharing your current LinkedIn (or any other) password with any third-party website.
Comments
Get your daily dose of tech news, reviews, and insights, in under 80 characters on Gadgets 360 Turbo. Connect with fellow tech lovers on our Forum. Follow us on X, Facebook, WhatsApp, Threads and Google News for instant updates. Catch all the action on our YouTube channel.
Further reading:
Hacking, Leaked Password, Leakedin, Linkedin, Password Breach, Password Security, Professional Networking, Social Networking
Related Stories
Popular on Gadgets
- Samsung Galaxy Unpacked 2026
- iPhone 17 Pro Max
- ChatGPT
- iOS 26
- Laptop Under 50000
- Smartwatch Under 10000
- Apple Vision Pro
- Oneplus 12
- OnePlus Nord CE 3 Lite 5G
- iPhone 13
- Xiaomi 14 Pro
- Oppo Find N3
- Tecno Spark Go (2023)
- Realme V30
- Best Phones Under 25000
- Samsung Galaxy S24 Series
- Cryptocurrency
- iQoo 12
- Samsung Galaxy S24 Ultra
- Giottus
- Samsung Galaxy Z Flip 5
- Apple 'Scary Fast'
- Housefull 5
- GoPro Hero 12 Black Review
- Invincible Season 2
- JioGlass
- HD Ready TV
- Latest Mobile Phones
- Compare Phones
Latest Gadgets
- Honor Play 80
- Nord 6
- Honor X80i
- Honor Play 80 Pro
- Redmi Note 15 SE 5G
- Redmi A7 Pro
- OPPO K15 Pro
- OPPO K15 Pro+
- Xiaomi Book Pro 14
- MacBook Neo
- Vivo Pad 6 Pro
- Lenovo Legion Y700 Gen 5
- boAt Valour Watch 1R
- Xiaomi Watch S5
- Xiaomi QLED TV X Pro 75
- Haier H5E Series
- Asus ROG Ally
- Nintendo Switch Lite
- Haier 1.6 Ton 5 Star Inverter Split AC (HSU19G-MZAID5BN-INV)
- Haier 1.6 Ton 5 Star Inverter Split AC (HSU19G-MZAIM5BN-INV)
© Copyright Red Pixels Ventures Limited 2026. All rights reserved.